Videos
Check out our video library AppCheck defending against newest ransomware, automatic recovery and real-time backup.


2024. 04. 21. 33
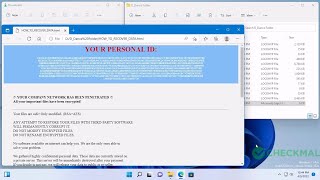
Black Kingdom Ransomware (.DEMON)


2024. 04. 19. 146
Stop Ransomware (.iiof)

2024. 04. 16. 180
MedusaLocker Ransomware (.lockhyp)


2024. 04. 12. 168
Phobos Ransomware (.id[<Random>-2994].[antich154@privatemail.com].Elbie)


2024. 04. 11. 171
Ransomnix Ransomware (.enc)


2024. 04. 06. 272
RURansom Ransomware (<Original Filename>.<Original Extension> / Пол…


2024. 04. 03. 322
Stop Ransomware (.qbaa)


2024. 03. 28. 278
CryptoJoker Ransomware (.fully.fucked / .partially.fucked)


2024. 03. 26. 287
GlobeImposter Ransomware (.charlie.j0hnson)


2024. 03. 24. 287
Pandora Ransomware (.pandora)


2024. 03. 21. 413
Stop Ransomware (.vyia)


2024. 03. 20. 406
Cryakl Ransomware (email-vegclass@aol.com.ver-CL 1.2.0.0.id-<Random>-<…