Videos
Check out our video library AppCheck defending against newest ransomware, automatic recovery and real-time backup.


2024. 04. 25. 18
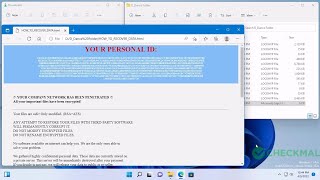
Cordless Ransomware (<Original Filename>.<Original Extension>)


2024. 04. 21. 42
Black Kingdom Ransomware (.DEMON)


2024. 04. 19. 169
Stop Ransomware (.iiof)

2024. 04. 16. 205
MedusaLocker Ransomware (.lockhyp)


2024. 04. 12. 174
Phobos Ransomware (.id[<Random>-2994].[antich154@privatemail.com].Elbie)


2024. 04. 11. 175
Ransomnix Ransomware (.enc)


2024. 04. 06. 278
RURansom Ransomware (<Original Filename>.<Original Extension> / Пол…


2024. 04. 03. 329
Stop Ransomware (.qbaa)


2024. 03. 28. 281
CryptoJoker Ransomware (.fully.fucked / .partially.fucked)


2024. 03. 26. 291
GlobeImposter Ransomware (.charlie.j0hnson)


2024. 03. 24. 291
Pandora Ransomware (.pandora)


2024. 03. 21. 415
Stop Ransomware (.vyia)